Review of Kaspersky Labs Report Confirms OPC Foundation’s Transparent, Open Source OPC UA Implementations Strategy Improves Security
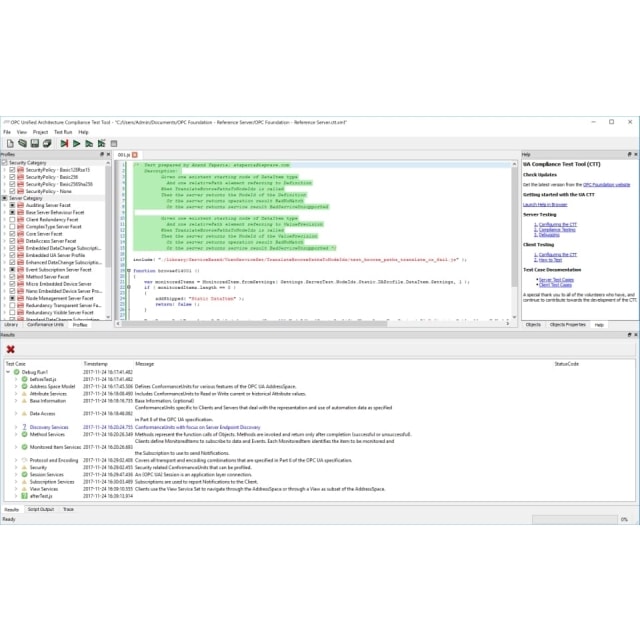
The Kaspersky Labs report issued on May 10th, 2018 has garnered a lot of media attention based on its claim of having identified 17 security issues in some OPC UA implementations. A detailed description of the 17 issues can be found at https://opcfoundation.org/security/. The OPC Foundation has and continues to be committed to ensuring the OPC UA standard provides the highest levels of security and as such has reviewed the claims made in the Kaspersky report.
The OPC Foundation has found that:
- Eight issues were associated with an OPC Foundation ANSI-C sample server application that was provided with the ANSI-C stack code in GitHub. These issues did not affect the ANSI C stack itself or products based on commercial SDKs. Nevertheless, all issues have been fixed.
- Six issues were associated with the OPC Foundation server enumerator (LDS). These were fixed in 2017 and a CVE was published. These issues were not exploitable remotely.
- Three issues affected some products in the field. Specifically: a.) One issue was specific to a product from a vendor who published a CVE in 2016; b.) The second issue is specific to a product from a vendor who is working on a fix and will report it to US ICS CERT as soon as possible; c.) The third issue affected a legacy .NET stack that was promptly fixed by the OPC Foundation in 2017. OPC users were notified of this issue via a CVE in 2017.
In addition, to alleviate potential confusion the Kaspersky Labs report may have created about the strong security the OPC UA standard offers, the OPC Foundation emphasizes that:
- The OPC UA software eco-system is composed of multiple commercial OPC UA SDK/Toolkit vendors that offer well tested and well documented products.
- The vast majority of OPC UA products are based on these commercial OPC UA SDK/Toolkits and are not affected by the issues with the ANSI-C sample server application published on GitHub.
- The OPC Foundation works cooperatively with vendors to have the open source code base tested by external security organizations and have those results incorporated into GitHub.
The broad adoption of OPC UA on a global basis reflects the market’s deep need for secure, open data connectivity and interoperability in manufacturing and beyond. Fortunately, this means that the OPC UA standard and its various open-source implementations are continuously subjected to close scrutiny by many in the large and active OPC UA community; something the OPC Foundation openly welcomes as this only makes the open-source implementations better.
Detailed information on the process for managing security issues can be found at https://opcfoundation.org/security/. The OPC Foundation is committed to addressing all issues as they arise, to working with OPC vendors to ensure that software is patched quickly, and to notifying OPC users about the issues and the fixes.
This process of continuous improvement based on open source software is a major reason why OPC UA is so successful in market today. The OPC Foundation will continue to provide its users with the robust and secure foundation that they expect from a key industrial interoperability standard.