Save costs and time, increase security: With the RFID employee ID card
RFID cards produced in the billions and used for more than 20 years cannot lie: Contactless cards are a successful invention! The spectrum of possible applications is broad – from car rental to access control. For every letter in the alphabet at least one application area can be found. The RFID card owes this success to the high flexibility of the card design. The smart interior – the RFID chip and antenna – is the technological focus.
AEG ID specializes in the development and production of RFID cards and keyfobs in the LF, HF and UHF frequency ranges, as well as combination solutions. Although billions of RFID cards are in use, 100% reliable hardware is essential, especially in security-relevant authentication processes, such as machine activation. RFID & Wireless IoT Global spoke to Simon Arch, Marketing and Sales Director, AEG ID, about how an RFID application can be integrated on machines by plug-and-play.
Simon Arch, Marketing & Sales Director at AEG ID in an interview with RFID & Wireless IoT Global.
As Efficient as Possible, as Safe as Necessary
A digital identity, stored on an RFID card, greatly simplifies authentication in a wide variety of applications. Depending on the level of security required, a simple tap on a reader is sufficient. If the security level can already be scaled via the transponder chip used, additional security hurdles can be created in combination with biometric or manual entries.
The result depends on the type of application: Employees can concentrate on their work instead of having to deal with time-consuming logins. Rental and leasing processes can also be started immediately and securely. Time control systems receive exact data and employees only enter the rooms and areas for which they are authorized.
The Overall System Creates Efficiency
The most modern and secure infrastructure based on an RFID application remains susceptible to manipulation and misuse if processes are not all coordinated with each other. For the production and coding of employee ID cards, processes must be defined and implemented to ensure the non-issuance of card data. Card management – from the allocation of rights to the end of the card life cycle – must also be specified. For this reason, it is important to implement an overall concept: In addition to the security aspects, the focus is on process optimization and scalability, as well as investment protection and future-proofing.
Standards for the Use of Contactless Cards
The LF, HF, and UHF chips used by AEG ID are standardized according to the globally valid standards ISO14443 or ISO15693 as well as ISO/IEC18000. The internationally applicable standards specify the physical properties as well as the radio frequency and modulation methods to be used. The structure of communication and the transmission protocol for contactless data exchange via the air interface are also defined.
Range, Lifespan and Chip Selection
Depending on the LF or HF technology used, RFID cards have clearly defined reading ranges in accordance with the ISO standards applied. The actual range in a realized application depends on national legislation, the working environment of the antenna, and the specific operational purpose. This clearly defined reading zone is intended to provide additional physical security.
A user must always be physically close to the reader with his/her card. This makes it more difficult to intercept radio communications via the air interface. The life cycle of a card depends on the RFID chip used and can amount to several hundred thousand write cycles. The life cycle of a card also depends on the card material used, such as PVC, PET, or PETG.
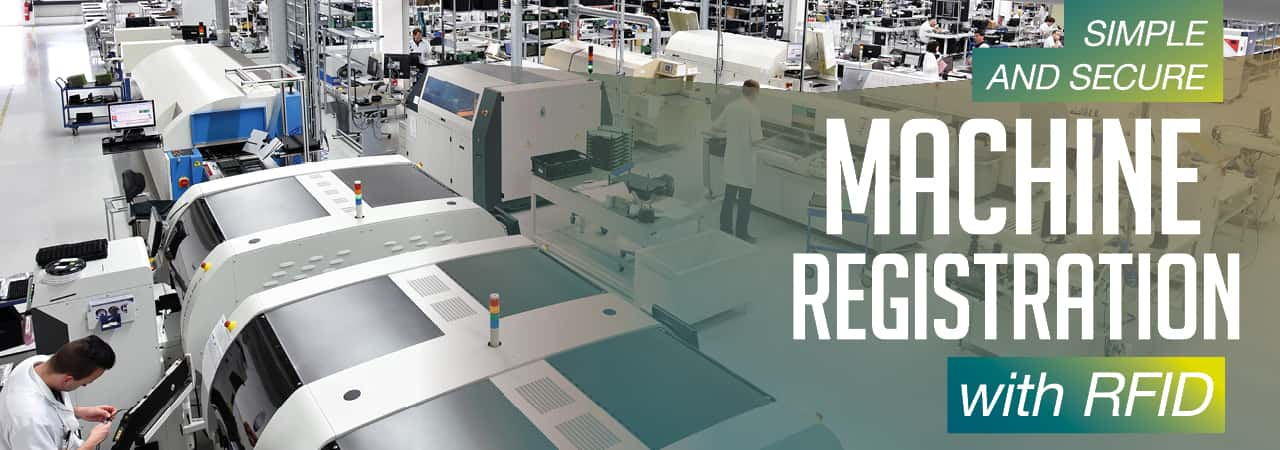
In Demand Worldwide: Machine Registration with RFID Cards
Production machines are costly assets. Passwords are usually used to protect them from maloperation. Machine operators, shift supervisors, or maintenance staff authenticate themselves via password entry. What sounds logical often works differently in practice. "It's not unusual for the operator password to be known by large sections of the workforce just a few days after a new machine is put into operation," reports Simon Arch from experience.
It is virtually impossible to trace which employee signed on to the machine and started a production order. The solution to this challenge, according to Simon Arch, can be found in the pocket of almost any employee worldwide: The employee ID card.
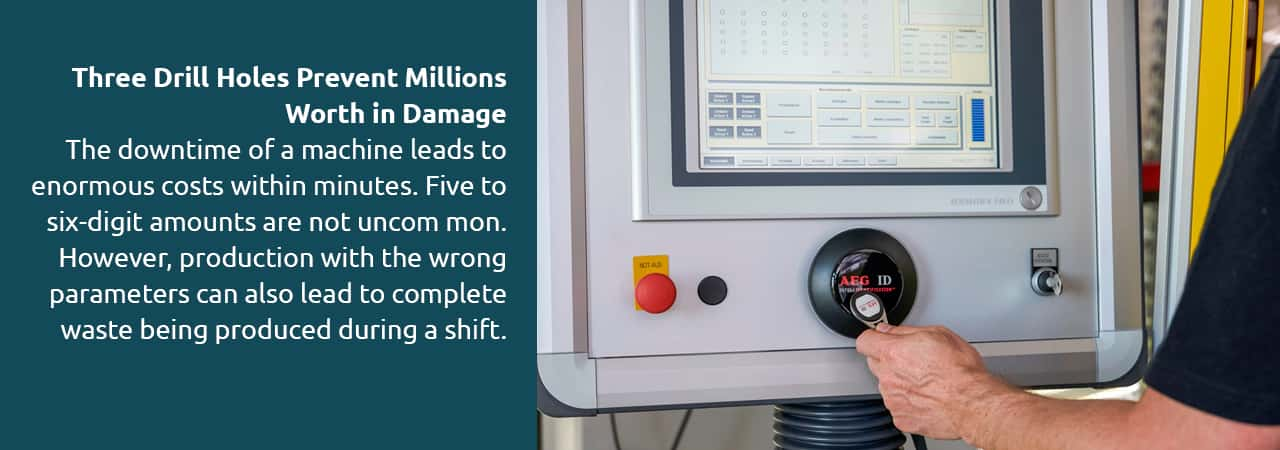
Three Drill Holes Prevent Millions Worth in Damage
"Production lines, for example in electronics manufacturing, are designed for maximum availability. The downtime of a machine leads to enormous costs within minutes. Five to six-digit amounts are not uncommon. However, production with the wrong parameters can also lead to complete waste being produced during a shift,” explains Simon Arch and continues: "Whenever such a case occurs, the question arises: Who operated the machine? If all employees use the same password, this question cannot be answered".
Many industrial companies around the world are currently looking into this question and are searching for an efficient, digital solution. The particular challenge here is that it must be an easy-to-install retrofit solution.
"No company is going to buy a completely new machine just to get an RFID-based authentication solution. In fact, it is not even possible to carry out extensive retrofitting work on running production machines," says Simon Arch, describing the requirements.
Upgrading Machines During Operation
AEG ID's solution is designed so that only three holes need to be drilled to attach an RFID reader directly to a machine. "This is true plug-and-play. Everything can be mounted and connected without having to switch off the machine. No complex wiring is necessary – a USB connection for power supply and data communication is sufficient".
Existing employee ID cards are used as an identification medium. The reader itself is recognized via the HID interface as a virtual keyboard on the machine's computer. If a machine operator now holds their RFID employee ID card against the reader, the reader writes the employee ID in any open text window in any system – be it Windows, Linux or other systems.
"No additional software or middleware is required. It is precisely these aspects that are crucial: An installation within minutes and immediate usability are convincing more and more users," says Simon Arch.
Feedback in Magenta, Blue, Green...
AEG ID focuses its retrofit solution on cost efficiency and easy integration. However, this does not rule out individualizing the solution according to the customer's requirements. "We produce all identification media such as cards and keyfobs as well as the readers from the chip upwards. This gives us a wide scope for the individual design of the components. The retrofit set for machine authentication includes the ARE DT1 reader.
It has an LED that emits a ring-shaped light signal as soon as a transponder is detected. The desired color can easily be customized. There is also the option of placing an individual design in the center. Just because the solution is cost-effective overall does not mean that customers have to do without these aspects of their brand presentation."
A Smartphone on the Machine? No Thanks!
Why can't an NFC-enabled smartphone also be used? "We have often heard this question. But the answer in such an authentication application is: Under no circumstances! Security could never be guaranteed. Employees install apps on their smartphones, and may even dial into insecure WiFi networks privately - a risk that no IT department would be willing to take," emphasizes Simon Arch. Nevertheless, he definitely regards the NFC benefit in the production environment as added value.
"For example, if a production manager uses an in-house smartphone or tablet to log on to a machine, NFC can act as an interface to visualize and edit production information or machine configurations on a mobile device. But for pure authentication of machine operators, the RFID employee ID card is and remains the best – and only – choice."
Source: RFID & Wireless IoT Global, Special Edition Wireless IoT Technology 2020